From Dubai to Donetsk: The Kyrgyzstan–UAE Transit Nexus in Russia’s Clandestine Starlink Supply Chain
Following the outbreak of the full-scale Russo-Ukrainian war, the Starlink satellite communication system became a critically important element of tactical and operational communications’ tool on the battlefields of Ukraine. Originally transferred to Ukraine by US officials as a means for ensuring stable connectivity, Starlink’s unique technical characteristics soon made it not only a tool of strategic importance but also an object of attempted use by Russia. Authoritative Russian information outlets openly admitted in 2024 that Russian armed forces were, in fact, frequently using Starlink systems in Donetsk Oblast in Russian occupied territories in eastern Ukraine.
By late 2025, individual episodes involving the use of Starlink by Russian forces had become a common trend that could no longer be ignored. According to Ukrainian officials, Russian units were using Starlink terminals to coordinate operations and control UAVs (unmanned aerial vehicles), including the so-called “killer drones.” In response, Kyiv introduced a verification mechanism – the so-called “white list” system – under which only verified Ukrainian devices could be activated. By early 2026, Ukrainian authorities announced that they had reached agreements with SpaceX to block the unauthorized use of terminals by the Russian military.
This resulted in the blocking of unverified terminals and prompted investigative reports into the possible involvement of third countries in facilitating the re-export or transit of Starlink equipment to Russia. At the forefront of these countries involved in the clandestine Russian effort was the Central Asian country of Kyrgyzstan. Crucially, the issue appears to be less about mere “physical access” to the hardware than about registration and network authorization. The fact that Russian forces were able to operate Starlink systems suggests that supply channels were intertwined with activation mechanisms and the circumvention of restrictions through third-party jurisdictions.
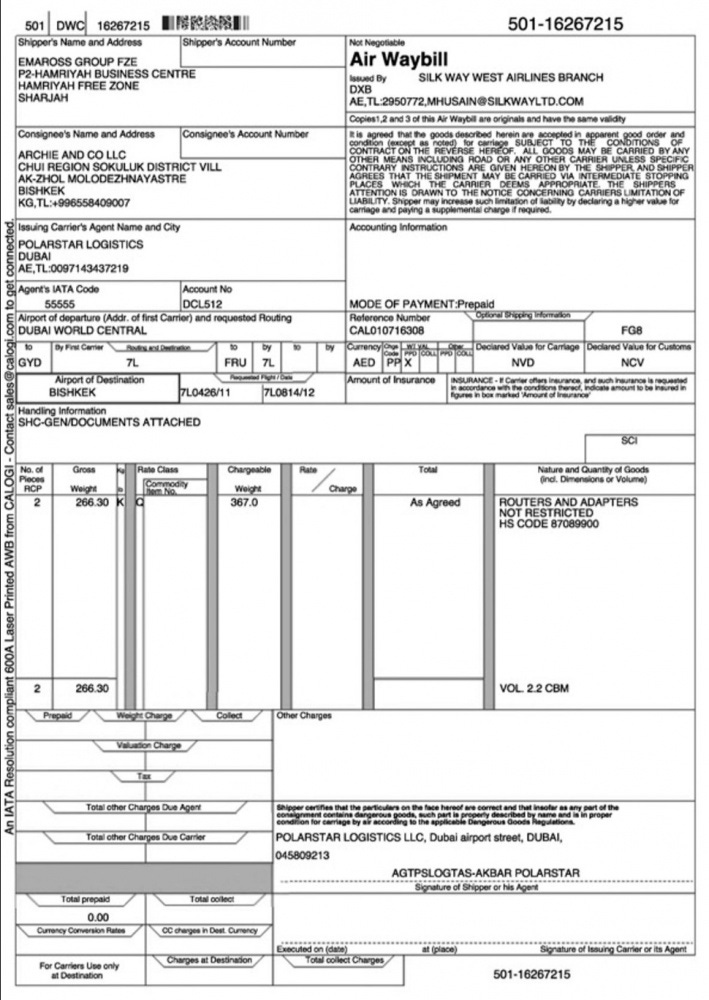
*Image above: Starlink Shipments with Emaross Cargo stickers
The Air Waybill Trail to Bishkek
Several investigative reports identified a specific shipment recorded under Air Waybill No. 501-16267215, dated May 10, 2024. The documentation lists the cargo as “routers and adapters not subject to restrictions,” ostensibly outside the scope of sanctions. However, the shipment was classified under HS code 87089900—corresponding to automotive parts rather than telecommunications equipment—and transported from Dubai World Central (UAE) to Bishkek (Kyrgyzstan). This discrepancy is analytically significant: misclassification under a non-sensitive customs code can reduce regulatory scrutiny and facilitate the movement of controlled or dual-use goods. According to an investigation by Nordsint, Starlink terminals subsequently appeared in Russian conformity registries, indicating likely downstream redistribution.
According to several investigative reports, three main actors were involved in the operational and logistical mechanism:
· Emaross Group FZE (UAE) – founded in 1994, the firm specializes in sourcing, transporting, and delivering goods, including both new and used vehicles, textiles, auto parts, and other freight categories, with capabilities for ocean, air, and land freight – appeared in customs documentation as the manufacturer; the company, however, stated that it only specializes in logistical and trans-shipment operations. The episode resulted in an internal investigation, discovering that the Starlink equipment that ended up in Russia had been shipped to Kyrgyzstan.
· Archie and Co LLC (Kyrgyzstan) – registered in Ak-Jol village (Chuy region), the company, whose declared business activity is “wholesale non-specialized trade”, was listed as the consignee/recipient of the above-mentioned cargo from the UAE, whose broad commercial classification, rural registration, and the lack of sectoral specialization made it an ideal actor for such transshipment. Importantly, the use of such an opaque actor provides de facto no direct evidence that could directly implicate the Kyrgyz government, whereas the structural characteristics of such entities make them suitable as buffer nodes in re-export operations.
· Polarstar Logistics – the carrier identified on the air waybill was a Uzbekistan-originated company with a Dubai link, under US sanctions at the time of shipment (it was added to the list in February 2024) – which was described by Emaross as “an active logistics agent within the UAE infrastructure”. Emaross explained the discrepancy in HS codes as a “technical administrative error” by Polarstar’s forwarder, who had used an outdated air waybill template for automotive components. The involvement of a sanction-exposed logistics operator raises compliance questions and suggests that high-risk transport intermediaries may play a functional role in Russia-oriented trade corridors.
Why the Middle East – Central Asia Link?
Understanding how Starlink systems ultimately appeared on Russian frontlines in Ukraine requires recognition as to why the “Kyrgyz case” is not an isolated incident, but is part of a broader sanctions-evasion network, involving multiple regional actors in Central Asia – including Uzbekistan - working with Russia-aligned logistical hubs in the Greater Middle East. Since 2022, Central Asia has seen a significant increase in a covert system of re-export flows back to Russia. Although much of this trade is lawful, investigative reporting and trade data patterns indicate that certain categories of high-technology goods have transited the region before reaching Russian end users. In this context, Kyrgyzstan—and Central Asia more broadly—possesses several structural characteristics that make it an effective transit node for smuggling high-tech goods within complex, multi-layered supply chains.
A. Membership in the Eurasian Economic Union (EAEU) and absence in the international sanction lists facilitate Kyrgyzstan`s ability to conduct cross-border trade with Russia.
B. Flexible wholesale trade registration: Kyrgyz law allows companies to choose broad business activity codes (including wholesale non-specialized trade), and this form of business registration is relatively straightforward and flexible.
C. Limited enforcement capacity relative to major Western export hubs. Analysts note that resource constraints, underdeveloped strategic trade control systems, and weak oversight of complex financial crimes have hindered the effective implementation of sanctions and regulatory measures.
D. Kyrgyzstan’s strategic geographic position between Russia and China facilitates multimodal transit routes. At this juncture, it is important to note the role of China, whose growing economic footprint in Central Asia adds complexity to both actual and future sanction evasion mechanisms. In the future, increased regional connectivity through Chinese logistics corridors may further complicate monitoring mechanisms.
The inclusion of the United Arab Emirates (UAE) in this configuration further complicates the picture. The UAE’s high cargo throughput, well-developed system of free trade zones, sophisticated re-export ecosystems, and its non-sanctioned status collectively strengthen the Central Asia–Middle East scheme. Together, these factors create a multi-layered buffer system in which global logistics origins are followed by regional transit jurisdictions.
Conclusion
The Kyrgyzstan–UAE episode in the Starlink supply chain underscores a profound transformation in the architecture of international sanctions: it is abundantly clear that existing sanctions regimes are no longer limited to restricting physical flows of goods; they increasingly operate at the intersection of hardware, software, licensing, and network authorization. At the same time, the Starlink case demonstrates that even when advanced technologies physically reach a sanctioned environment through multi-layered transit corridors and buffer jurisdictions, their operational effectiveness ultimately depends on activation mechanisms controlled by origin-state actors. For example, the ability of Ukraine and SpaceX to introduce verification mechanisms and block unauthorized terminals illustrates that, for the time being, the West retains significant control and leverage over critical digital infrastructures and dual-use technologies.
In the long term, the strategic implications of this episode may prove even more consequential. The exposure of transit corridors through jurisdictions such as Kyrgyzstan and the UAE, combined with the demonstrated vulnerability of foreign-supplied systems to remote restriction, is likely to accelerate efforts by Russia, China, and other non- or anti-Western powers to prioritize “sovereign” technological ecosystems. These efforts encompass domestically controlled satellite communications, payment systems, semiconductor production, and digital infrastructures insulated from Western regulatory reach. In other words, while the current system enables Western actors to impose meaningful constraints, it simultaneously incentivizes technological decoupling. The Starlink case, therefore, should not be viewed merely as another episode of sanctions evasion; rather, it signals a broader structural shift toward a fragmented global technological order in which control over activation, standards, and digital governance is becoming as strategically significant as control over physical supply chains.
About the Author
Dr. Sergey Sukhankin is a Senior Fellow at The Saratoga Foundation specializing in Russian military and security affairs, as well as Russo-Chinese relations. He is also an Advisor at Gulf State Analytics (Washington, D.C.) and Fellow at the North American and Arctic Defense and Security Network (Canada).
Thank you for your support! Please remember that The Saratoga Foundation is a non-profit 501(c)(3) organization. Your donations are fully tax-deductible. If you seek to support The Saratoga Foundation, you can make a one-time donation by clicking on the PayPal link below! You can also subscribe to our website to support our work.
https://www.paypal.com/donate/?hosted_button_id=XFCZDX6YVTVKA